



One of the methods to crack WPA/WPA2 wireless encryption key is by using a wordlist and then using this wordlist to Bruteforce the key of the Wi-Fi access point.
Wordlist: a collection of passwords stored in plain text. Basically, it’s a TXT file with a bunch of random passwords in it.
The problem is, if the key isn’t in the wordlist, you won’t be able to find the key to the wireless access point.
In this case, you either have to use another method or use a larger wordlist that contains capital letters, numbers, and symbols.
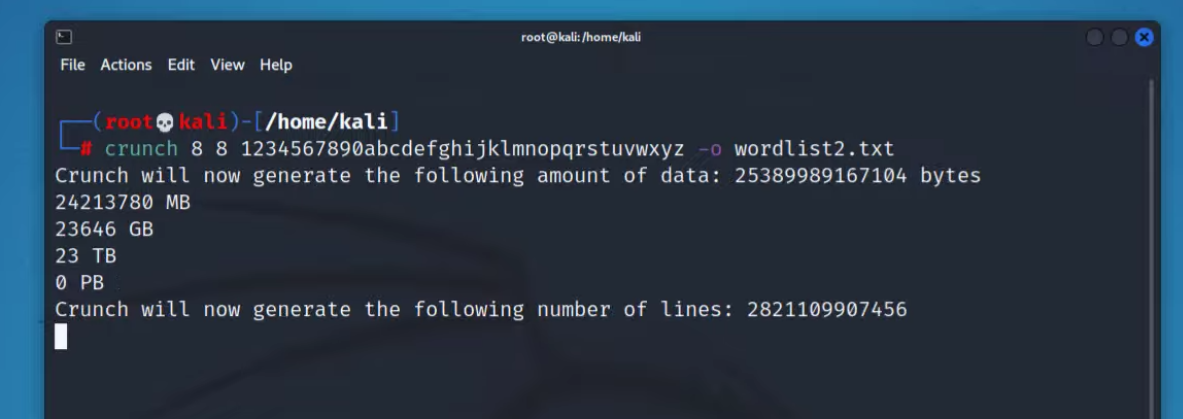
But creating a large wordlist takes a lot of disk space.
Please keep in mind, I am attacking my own Wi-Fi Access Point. If you want to test the attack, please perform the attack against your own network.
if you want to generate a wordlist of 8 characters with all small letters from a to z, you need at least 1 TB of storage.

To solve this issue, we are going to generate a wordlist using crunch. But instead of saving the wordlist to a file, we are going to let crunch display the results or the wordlist combination on the screen. Then we will redirect the terminal output to aircrack-ng to find the correct key.
Keep in mind, we are not saving the wordlist to a file.
All we are doing is redirecting the output of crunch to aircrack-ng so that it tries every single generated combination on the fly.
1. Alfa AWUS036ACH
2. Alfa Network AWUS036NHA